- Intro to IAM
- What is MFA?
What is Multi-Factor Authentication (MFA)?
Multi-Factor Authentication (MFA) refers to an authentication method in which a user is required to use two or more authentication factors before being granted access to the requested resource. An authentication factor is a mechanism used to perform authentication, such as a username and password, a one-time code, a smart card, etc. By implementing an MFA strategy, when a user signs in to leverage resources, the apps, web-server, etc. challenge them with a second-factor or further authentication factors (hence the name). These multiple authentication factors, which can include biometrics like, for example, facial recognition, help systems have higher confidence in the identity of their users. This way, the MFA method contributes to diminishing the likelihood of impersonation attacks and credential theft.
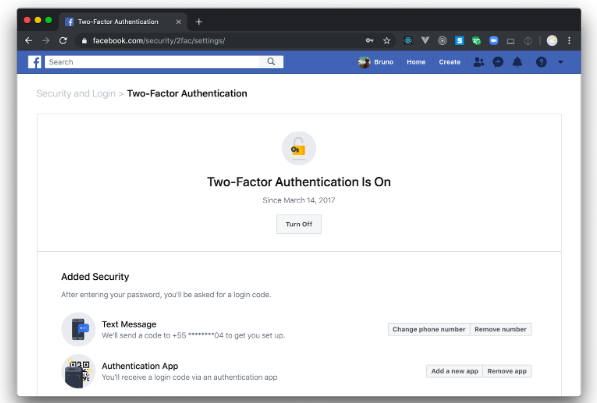
You have probably already seen at least one type of MFA in action if you ever received a temporary code sent through SMS to your mobile device (i.e., smartphone/mobile phone). The combination of traditional username and password and SMS codes is an example of two-factor authentication, a subset of MFA. For example, if you have a Facebook or a Google account, you have probably seen a message from one of these services encouraging you to activate Two-Factor Authentication (2FA). And, if you have enabled this feature in one of them, after providing your username and password, you will likely have received a temporary, disposable code sent to your mobile device that the service asked you to input to complete the authentication process. The whole process to login used more than one factor to authenticate the user’s identity (password and the SMS code, aka passcode).
Note: If you use Single Sign-On, Multi-Factor Authentication is highly recommended since it mitigates the potential risks of identity theft.
What are the Different Types of Factors on MFA?
There are many different examples of factors a system secured with MFA can use to increase its confidence in the identity of their users.
- A password
- One-time, temporary codes, sent to a mobile app
- OTP (one-time password) that can be used with a web app
- Biometric authentication in the form of a fingerprint or face of a user
- QR codes, smart card
Because there are many different types of factors available for end-user authentication, security specialists have organized them into three categories:
Knowledge: This category refers to authentication factors where users have to prove they know something (like a password or the answer to a security question - although the latter is being used less frequently as online trawling of user data has made this method less secure).
Possession: The possession factor requires users to prove they own something (like a mobile device where they can receive an SMS code).
Inheritance: The last category is about factors where users have to verify their identity through biometrics (for example, a retina scan or facial recognition or a fingerprint scan).
Step-Up Authentication
One mechanism that modern applications are starting to adopt to increase their security is the use of "Step-Up Authentication" as a use case. This mechanism relies on MFA to increase security in specific parts of an application. In short, an application challenges end-users for extra factors only when they try to access resources that are more sensitive than others.
For example, imagine a system that requires users to authenticate with their username and password to access customer data. Accessing this information might be a common task that some employees do on a daily basis, and you might consider this activity non-sensitive. However, you might consider updating this information or accessing further details about customers (like contract details) a sensitive task that requires increased protection. In this situation, using Step-Up Authentication would be an ideal fit. When users click on the "edit" button, the system could challenge them with another factor to decrease the chances of unauthorized access.
This approach tends to provide a better balance between user experience and data security. That is, instead of challenging users with a different factor every time they sign in, you can let them do their daily jobs and secure only the data that needs more protection.
Implementing Multi-Factor Authentication with Auth0
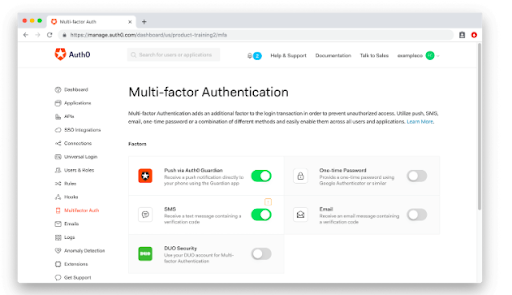
Auth0 is an identity platform used by thousands of customers in every market sector. It allows them to centralize identity management for their apps, and it ships with MFA at its core. That is, the process of implementing MFA with Auth0 is a breeze, consisting of one or two simple steps:
Firstly, sign in to your Auth0 dashboard, head to the Multi-Factor Authentication screen, and choose the factors that you want to enable. You can use as many factors as you want simultaneously.
Then, depending on the factors that you have activated, you might need to perform some additional configuration. After that, your apps will have increased security and be protected against threats.
Apart from Multi-Factor Authentication, Auth0 also supports step-up authentication, and the process of activating it is pretty straightforward too. To learn the details about how to use Auth0 to secure your apps with these authentication features, refer to the official documentation:
Want to learn more?
Keep reading at our Intro to IAM page to explore more topics around Identity and Access Management.
Table of contents